Become a MacRumors Supporter for $50/year with no ads, ability to filter front page stories, and private forums.
How to Encrypt a USB Flash Drive in macOS Mojave
- Thread starter MacRumors
- Start date
- Sort by reaction score
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
I just checked and it looks like these are saved in the local "login" Keychain by default, so they would not get backed up to iCloud as you mentioned. But that login Keychain would get backed up along with everything else in your Time Machine backup so that should have you covered.Note that saving the decryption key in keychain does not seem to back the key up to iCloud.
I have used iCloud Keychain for years and recently after rebuilding my MBP I was unable to decrypt a drive that had the key stored in keychain.
I just checked and it looks like these are saved in the local "login" Keychain by default, so they would not get backed up to iCloud as you mentioned. But that login Keychain would get backed up along with everything else in your Time Machine backup so that should have you covered.
Is there a way to force this to back up to iCloud?
Thanks
I played around with it, and it looks like you can copy the entry from the login Keychain and paste it into the iCloud Keychain. But instead of keeping the drive name, it changes it to the UUID # of the drive.Is there a way to force this to back up to iCloud?
Thanks
Here is the login Keychain entry.
I right clicked and copied it from login then right clicked and pasted in iCloud Keychain and it made the new entry you see here in the iCloud Keychain. Presumably this would sync along with everything else in the iCloud Keychain.
I have not tested if you delete this entry from login Keychain if this iCloud entry will unlock the drive.
I played around with it, and it looks like you can copy the entry from the login Keychain and paste it into the iCloud Keychain. But instead of keeping the drive name, it changes it to the UUID # of the drive.
View attachment 811310
Here is the login Keychain entry.
View attachment 811312
I right clicked and copied it from login then right clicked and pasted in iCloud Keychain and it made the new entry you see here in the iCloud Keychain. Presumably this would sync along with everything else in the iCloud Keychain.
I have not tested if you delete this entry from login Keychain if this iCloud entry will unlock the drive.
Thanks for your in depth analysis on this! I ran into issues with this and lost a drive of pictures (I had other backups so not a big deal). I like the privacy of having the drive encrypted but since losing the data I've been hesitant to use it on external drives.
If you want to encrypt some data on a flash drive (or other removable drive), another way to do this is to create an encrypted disk image on the drive. That way anybody can still mount and use it for other stuff, but you've also got a sub-section that's locked away.
This same principle can be applied to cloud services as well. I have a bunch of sensitive account recovery stuff I keep backed up in Dropbox, but inside a heavily-encrypted disk image file. You still get the benefits of backup and syncing but without leaving your data out in the open on the service you're using.
This same principle can be applied to cloud services as well. I have a bunch of sensitive account recovery stuff I keep backed up in Dropbox, but inside a heavily-encrypted disk image file. You still get the benefits of backup and syncing but without leaving your data out in the open on the service you're using.
Thanks for your in depth analysis on this! I ran into issues with this and lost a drive of pictures (I had other backups so not a big deal). I like the privacy of having the drive encrypted but since losing the data I've been hesitant to use it on external drives.
Good you had backups! I think that especially with little removable devices like USB drives, it's crucial to follow the wisdom (as you did) that nothing important should ever exist on only one drive.
Is flash storage on a USB the same type of storage technology as on a SSD? Thus, better to format in APFS.
Yes, the technology is basically identical. The speed differs between flash drives and SSDs for a number of reasons, but the tech is the same. APFS is more optimized for SSDs, but it's better than HFS+ in numerous other ways. It's also the best option for ye ol' spinning rust drives as well. Apple has quietly added defragmentation support to APFS, which is only relevant on magnetic drives.
I'd add the strong caution that not all USB flash keys are well-made; in fact, I would go so far as to say most aren't. SSDs tend to have much better reliability both through better control mechanisms and through higher-grade flash memory to begin with. SSDs probably also have more blocks set aside for recovery of bad blocks--who knows what USB flash drives have.
I'm sure the distinction lessens with top-tier manufacturers, but even there a Samsung USB flash stick is just not going to be the same as an 860 PRO. To say nothing of the no-brand (or rebranded) USB sticks you buy in a checkout line somewhere. But in the latter case you shouldn't be trusting cheap USB sticks with your data in the first place.
I'm not sure what implications bad USB sticks have for choice of formatting. Even with those APFS is probably better.
APFS is a superior format to HFS+ in many ways. It should be the preferred format on all newly-formatted macOS disks, unless backwards-compatibility with older versions of macOS/OS X/Mac OS X is required. Also, HFS+ can be read on Windows and Linux with the proper software installed, so that's another consideration.I'd add the strong caution that not all USB flash keys are well-made; in fact, I would go so far as to say most aren't. SSDs tend to have much better reliability both through better control mechanisms and through higher-grade flash memory to begin with. SSDs probably also have more blocks set aside for recovery of bad blocks--who knows what USB flash drives have.
I'm sure the distinction lessens with top-tier manufacturers, but even there a Samsung USB flash stick is just not going to be the same as an 860 PRO. To say nothing of the no-brand (or rebranded) USB sticks you buy in a checkout line somewhere. But in the latter case you shouldn't be trusting cheap USB sticks with your data in the first place.
I'm not sure what implications bad USB sticks have for choice of formatting. Even with those APFS is probably better.
Since I generally need to use my USB sticks on both Windows and Mac (plus occasionally Linux), what I do is create a Veracrypt image on an exFAT-formatted USB stick. I leave enough room for the Mac installer on there - you can make Veracrypt containers “portable” (self-contained) for Windows, but for Mac you need to have Veracrypt installed on the computer.
It’s surprising, but there are still occasions when a USB stick is easier and faster than working over the network.
BTW if you aren’t familiar with Veracrypt - it’s the maintained successor to the last audited version of TrueCrypt.
I encrypted my 10 TB external HDD in veracrypt. ExFAT formatted. It mounts fine in windows but when I plug in the encrypted disk into macbook (running OS mojave), I get the error "the disk you inserted was not readable by this computer". If I open veracrypt for mac and try to mount the disk, I get the error "hdiutil: attach failed - no mountable file systems"
I have FUSE for macOS installed, before installed VeraCrypt.
The partition shows as Microsoft Basic Data in disk utility command output on mac.
No response on their main forum or subreddit. This software doesn't seem to have much support.
That doesn't make it a 'good' choice - and it's not, for the reasons given by others.Disagree. It’s an official feature in Mojave and one can still follow the exact same options despite it being in dark mode.
Hi everyone,
I would really appreciate your help.
I tried to encrypt my usb drive but no joy. When I drop down erase options in Disk utility it would not give me encrypt one. Please look at the attached photo and advise me what to do.
When I drop down erase options in Disk utility it would not give me encrypt one. Please look at the attached photo and advise me what to do.
I would really appreciate your help.
Thank you very much in advance
I would really appreciate your help.
I tried to encrypt my usb drive but no joy.
I would really appreciate your help.
Thank you very much in advance
Attachments
Hi everyone,
I would really appreciate your help.
I tried to encrypt my usb drive but no joy.When I drop down erase options in Disk utility it would not give me encrypt one. Please look at the attached photo and advise me what to do.
I would really appreciate your help.
Thank you very much in advance
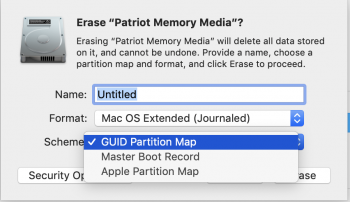
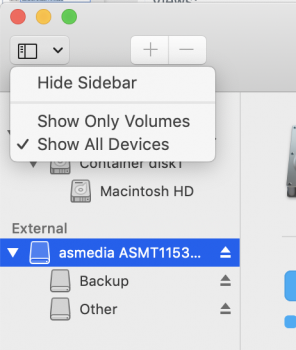
Go to the scheme dropdown and change it from MBR to GUID then the encrypted options will appear.
Thank you,View attachment 829077
Go to the scheme dropdown and change it from MBR to GUID then the encrypted options will appear.
There is no "scheme dropdown" option as it is possible to see on the image I uploaded above.
Thank you very very much!!!View attachment 829082
Make sure you have enables show all devices, then select the drive itself like in my photo and not one of the volumes below it.
It works now!
I do appreciate your help so much. Thank you!
Register on MacRumors! This sidebar will go away, and you'll see fewer ads.